 Apple computers are not immune to malware vulnerabilities. A new form of malware called “ransomware” is targeting Apple’s Mac OS X operating system. Ransomeware is a computer virus that encrypts important data such as pictures, videos, music, and documents in order to “hold it for ransom” at an unsuspecting victim’s expense. If the victim pays the ransom then, hopefully, they would receive a key to decrypt their data, known as a decryption key. Unfortunately many times there is no decryption key and the victim loses not only their data but possibly up to $700 USD in ransom payment. The ransom payment transaction occurs using an anonymous payment method in order to conceal the identity of the scammer holding the data ransom so that there is no trace. Ransomware is usually spread via email attachments, peer to peer file sharing, and more recently removable devices such as external hard drives and USB flash drives.
Apple computers are not immune to malware vulnerabilities. A new form of malware called “ransomware” is targeting Apple’s Mac OS X operating system. Ransomeware is a computer virus that encrypts important data such as pictures, videos, music, and documents in order to “hold it for ransom” at an unsuspecting victim’s expense. If the victim pays the ransom then, hopefully, they would receive a key to decrypt their data, known as a decryption key. Unfortunately many times there is no decryption key and the victim loses not only their data but possibly up to $700 USD in ransom payment. The ransom payment transaction occurs using an anonymous payment method in order to conceal the identity of the scammer holding the data ransom so that there is no trace. Ransomware is usually spread via email attachments, peer to peer file sharing, and more recently removable devices such as external hard drives and USB flash drives.
While this is not the first time Apple computers have been vulnerable to malware attacks, such as the FBI virus a few years ago, a recent Reuters report revealed that ransomware was targeting Apple computers for the first time. Ransomware is already rampant on computers running the Windows operating system. Many variants of the trojan horse already exist such as Bitlocker, CryptoWall, Cryptorbit, and CryptoLocker or Crypto-malware. So far the ransomware has infected Apple computers via peer to peer file sharing networks using bit torrent.
There is no easy fix for the data that has been affected by the ransomware. Without the decryption key the data is scrambled to a point that it cannot be deciphered using current technology.
“The best way to protect your data from a ransomware attack is to have an archive backup of the important data on a computer” says South City Computer security expert Nestor Wheelock. “Because the archive is completely disconnected from the live file system the ransomware will not encrypt the data”. While this form of data backup service is complex and daunting to most computer users, South City Computer offers a service package that includes this type of backup service. If you need assistance setting up this type of backup service contact South City Computer or a local computer repair store near you.
 Earlier this year cyber security software company Kapersky announced the discovery of a cyber intrusion that affected many of it’s internal computer systems which initiated a large scale investigation. They believe the virus penetrated their systems through an email attachment sent to an employee at the company. From there the virus moved stealthily through the company’s computer network targeting it’s customer’s computer networks and collecting information. Instead of removing the virus Kapersky monitored the virus on their systems in an attempt to better understand its function and purpose.
Earlier this year cyber security software company Kapersky announced the discovery of a cyber intrusion that affected many of it’s internal computer systems which initiated a large scale investigation. They believe the virus penetrated their systems through an email attachment sent to an employee at the company. From there the virus moved stealthily through the company’s computer network targeting it’s customer’s computer networks and collecting information. Instead of removing the virus Kapersky monitored the virus on their systems in an attempt to better understand its function and purpose. Social media “click bait” targeting has become a big business in recent years. “Click-baiting” is when a publisher posts a link on a social media website like Facebook, Twitter, or Pinterest with a headline that lures people to click to see more, without telling them much information about what the user will really be taken to. Websites like BoredPanda, Buzzfeed, Reddit, College Humor, and Gawker (to name a few) use click bait headlines to lure users to embedded web content surrounded by advertisements. Click baiting has forced Facebook developers to re-evaluate their algorithm for what is considered relevant content, as currently the more clicks a link receives the more likely it is to appear in other users feeds. Wording a link with just the right message in order to get users to click out of the social media website is what “click baiting” is all about. While many of these links take users to relevant content (like this article), there are several new scams also using the tactic to infect computers with malware or attempt to steal personal information.
Social media “click bait” targeting has become a big business in recent years. “Click-baiting” is when a publisher posts a link on a social media website like Facebook, Twitter, or Pinterest with a headline that lures people to click to see more, without telling them much information about what the user will really be taken to. Websites like BoredPanda, Buzzfeed, Reddit, College Humor, and Gawker (to name a few) use click bait headlines to lure users to embedded web content surrounded by advertisements. Click baiting has forced Facebook developers to re-evaluate their algorithm for what is considered relevant content, as currently the more clicks a link receives the more likely it is to appear in other users feeds. Wording a link with just the right message in order to get users to click out of the social media website is what “click baiting” is all about. While many of these links take users to relevant content (like this article), there are several new scams also using the tactic to infect computers with malware or attempt to steal personal information. A new destructive virus known as Rombertik avoids detection from most anti-virus software by making a computer unusable by deleting key files on a computer and filling the hard drive with extraneous bytes of data in order to overwhelm the anti-virus software from detecting it.
A new destructive virus known as Rombertik avoids detection from most anti-virus software by making a computer unusable by deleting key files on a computer and filling the hard drive with extraneous bytes of data in order to overwhelm the anti-virus software from detecting it. 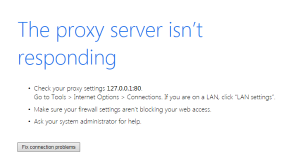 One of the more common computer issues we see because of malware is a misconfiguration Proxy Server connection setting in the browser. You may be able to do a quick fix to get your Internet connection back up and running, however if this has gotten set and you don’t recall doing it, this is probably because your computer is infected with malware or a virus.
One of the more common computer issues we see because of malware is a misconfiguration Proxy Server connection setting in the browser. You may be able to do a quick fix to get your Internet connection back up and running, however if this has gotten set and you don’t recall doing it, this is probably because your computer is infected with malware or a virus.